Catalan independence leaders accuse Spain of mass surveillance campaign
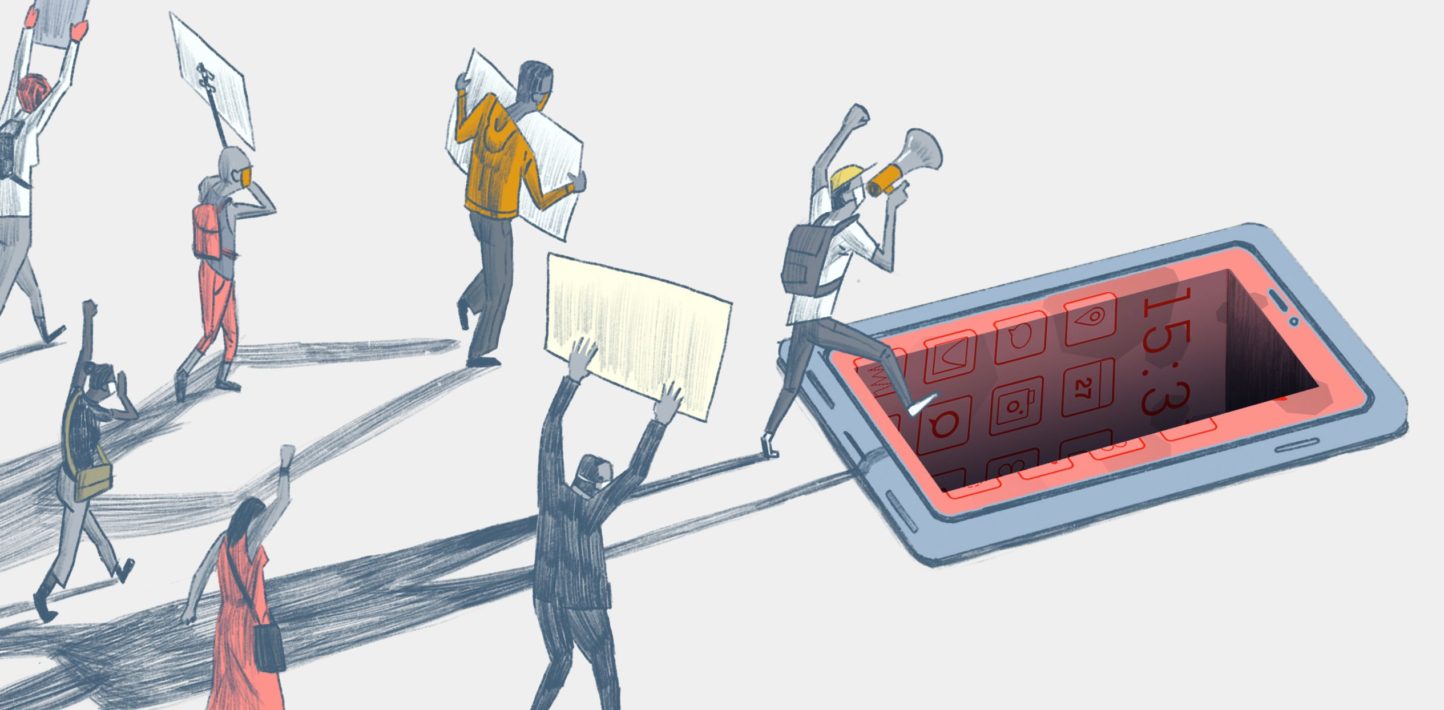
A new report suggests that the Spanish government used the controversial Pegasus software to monitor the phones of dozens of Catalan independence figures.

Incidents of phone hacks peaked between 2017 and 2020, when the push for Catalan
independence led to Spain's deepest political crisis in decades
Leaders of the movement for Catalan independence said on Monday that the Spanish government was spying on at least 65 people after a report by Canadian research center Citizen Lab found that the controversial Israeli spyware Pegasus had been installed on their phones.
The phones were allegedly hacked between 2017 and 2020, when relations between Barcelona and Madrid were at a low point following an independence referendum that Spain sought to quash.
The kind of espionage they are accusing the government of is illegal in Spain.
Who was targeted?
Pedro Sanchez of the Spanish Socialist Workers' Party (PSOE) has been Prime Minister since June 2018, after a successful motion of no confidence against former Prime Minister Mariano Rajoy. The software was installed on the phones when Rajoy was at the helm. It is not known if the government of Sanchez was informed at the change of power, though ex-Catalan leader Carles Puigdemont pointed the finger at both governments.
Those targeted include present Catalan leader Pere Aragones, who was deputy leader of the region at the time, ex-regional leaders Quim Torra and Artur Mas, as well as members of the EU and Catalan parliaments and of independent civil organizations.
"We have been spied on in a huge and illegal manner through software that only states can possess," Puigdemont tweeted.
"Politicians, lawyers and activists are all victims of the Spanish state's dirty war," he added.
What is Pegasus?
Pegasus was developed by the Israeli cyber-arms company NSO Group. It can switch on a phone's camera or microphone remotely, and can harvest the data of almost any smartphone running Android or iOS operating systems.
It first came to light in 2016 when it was discovered on the phone of a human rights activist being surveilled by the government of the United Arab Emirates, and has been criticized for its use against dissidents and other activists across the globe.
Security services in EU countries such as Estonia, Finland, and Germany have either used the software or begun negotiations to purchase it. The FBI in the United States had reportedly tested the software but decided against using it.
After years of tensions, the enmity between Madrid and Barcelona began to ease in 2020 after the Spanish government began talks with independence leaders and Socialist Prime Minister Sanchez pardoned nine jailed separatist leaders.
es/jsi (AP, AFP)
European Union institutions are failing to end the rampant human rights violations committed with spyware, Amnesty International said today, after the organization independently confirmed new attacks using Pegasus spyware against prominent Catalans.
New research by the Citizen Lab has revealed how scores of Catalan politicians, journalists and their families were targeted with NSO Group’s Pegasus spyware between 2015 and 2020. Technical experts from Amnesty International’s Security Lab have independently verified evidence of the attacks.
The Spanish government needs to come clean over whether or not it is a customer of NSO Group. It must also conduct a thorough, independent investigation into the use of Pegasus spyware against the Catalans identified in this investigation.Likhita Banerji, Amnesty International’s Technology and Human Rights Researcher.
Confirmed targets include Elisenda Paluzie and Sònia Urpí Garcia, who work with the Assemblea Nacional Catalana, an organization that seeks the political independence of Catalonia from Spain. Elisenda Paluzie is the current president of the group.
Catalan journalist Meritxell Bonet’s phone was also hacked in June 2019. She was targeted in the final days of a Supreme Court case against her husband Jordi Cuixart, an activist and former president of Catalan association Òmnium Cultural, who was sentenced on a charge of “sedition”.
Politician, university professor and Catalan activist Jordi Sànchez was extensively and persistently targeted with Pegasus from as early as September 2015 until July 2020. Between 2015 and 2017, he was president of the Assemblea Nacional Catalana. His phone was successfully compromised with Pegasus on 13 October 2017, days before his arrest by Spanish authorities on a charge of “sedition”.
In October 2020, Amnesty International Spain wrote to the Spanish government asking it to disclose information on all contracts with private digital surveillance companies which was not disclosed. Amnesty International Spain also later approached the Spanish Ministry of Defense, requesting information on Pegasus use from the National Intelligence Center. They responded stating that such information falls under classified subjects. NSO states that it only sells to governments and that its tools are meant to be used to combat serious organized crime and terrorism.
“The Spanish government needs to come clean over whether or not it is a customer of NSO Group. It must also conduct a thorough, independent investigation into the use of Pegasus spyware against the Catalans identified in this investigation,” said Likhita Banerji, Amnesty International’s Technology and Human Rights Researcher.
Amnesty International’s Security Lab peer reviewed forensic evidence from a sample of individuals first identified in the Citizen Lab investigation, and found evidence of Pegasus targeting and infection in all cases.
European Parliamentary Committee of Inquiry first meeting
The revelations come as a European Parliamentary Committee of Inquiry is set to hold its first meeting on Tuesday (19 April) into breaches of EU law associated with the use of Pegasus and equivalent spyware – a direct result of the Pegasus Project revelations in July 2021. Last week, Reuters reported that senior EU figures had been targeted with NSO Group’s Pegasus.
“We urge the European Parliament Committee of Inquiry to leave no stone unturned when documenting the human rights violations enabled by unlawful spyware, including by investigating these new revelations,” said Likhita Banerji.
“Governments around the globe have not done enough to investigate or stop human rights violations caused by invasive spyware like Pegasus. The use, sale and transfer of this surveillance technology must be temporarily halted to prevent further abuses of human rights.”
Amnesty International, alongside other civil society organisations, has previously documented the widespread and unlawful use of spyware against activists, politicians and journalists around the globe, including as part of the Pegasus Project.
In Europe, activists, journalists and other members of civil society have been unlawfully targeted in Belgium, France, Greece, Hungary, Poland, Spain and the United Kingdom.
NSO Group has not taken adequate action to stop the use of its tools for unlawful targeted surveillance of activists and journalists, despite the fact that it either knew, or arguably ought to have known, that this was taking place. NSO Group must immediately shut down clients’ systems where there is credible evidence of misuse of its tools.
UK-based Pegasus targets threaten
lawsuits against NSO, UAE and Saudi
Arabia
Lawyers for three civil society leaders say they plan to sue the Israeli firm and two countries in the High Court after their clients were hacked with Pegasus spyware

A photographic illustration shows a mobile phone near the NSO Group company logo in February 2022 in the Israeli city of Netanya (AFP)
By Dania Akkad
Published date: 19 April 2022 13:35 UTC | Last update: 2 hours 31 mins ago
Three UK-based civil society leaders have notified NSO Group, Saudi Arabia and the United Arab Emirates that they plan to sue them in the UK's High Court over allegations that the two countries used the Israeli firm's spyware against them, their lawyers said on Tuesday.
Lawyers for Yahya Assiri, a Saudi human rights defender, Anas Altikriti, head of the Cordoba Foundation, and Mohammed Kozbar, chairman of Finsbury Park Mosque, say their clients' mobile phones were hacked with Pegasus spyware between 2018 and 2020 while they were in the UK.
The hacking, say the lawyers with the London-based Bindmans lawfirm, was an invasion of their privacy rights and their clients are seeking to bring breach of privacy claims against the firm and Saudi Arabia and the UAE.
The three potential defendants were informed about this in letters sent in late February, but only the NSO Group has responded formally, the lawyers said in a statement on Tuesday.
Assiri, the former secretary general of the National Assembly Party (NAAS), a pro-democracy Saudi opposition party founded in 2020, said in a statement that abusive dictators will "not leave us to defend justice and rights without attacking us by any means".
"They will use everything, legal or illegal, to stop us and protect their interests, and now everyone can see and understand the reality," he said, adding that he was optimistic that the judicial system would "stand with us".
"Yes, they spy on us, have arrested our friends and tortured and killed some of them, but we believe that the side of justice and rights will prevail in the end."
Assiri, Altikriti and Kozbar were among 400 UK-based activists, academics, politicians and others whose phones were found on leaked list of numbers identified by governments using NSO Group's Pegasus spyware.
After stories based on the list, acquired by Amnesty International and journalistic consortium, Forbidden Stories, were published last summer as part of the Pegasus Project, nine of the UK-based individuals, including Assiri, Altikriti and Kozbar, whose numbers were found instructed Bindmans to investigate.
The "pre-action" letters sent on behalf of Assiri, Altikriti and Kozbar came after a subsequent six-month probe which was conducted in partnership with the Global Legal Action Network (GLAN), a UK-based legal NGO, and with support from Bill Marczak, a senior research fellow at Citizen Lab and Reckon Digitial, a UK-based technology consultancy. Further claims may follow, the lawyers said.
"The use of Pegasus spyware against these human rights defenders has made their work even more dangerous," said Siobhan Allen, GLAN legal officer and a consultant solicitor with Bindmans. "It is important to pursue judicial recognition that this should not have happened."
Middle East Eye is seeking comment from NSO Group, Saudi Arabia and the United Arab Emirates.
NSO Group's software targeted activists, journalists, politicians and executives. The US government,
Stephen Shankland
April 19, 2022

It's a doozy of a case of digital spying technology. Security researchers have revealed evidence of attempted or successful installations of Pegasus, software made by Israel-based cybersecurity company NSO Group, on 37 phones belonging to activists, rights workers, journalists and businesspeople. They appear to have been targets of secret surveillance by software that's intended to help governments pursue criminals and terrorists, and as the months go by, more and more Pegasus.
The most recent revelations are that Pegasus infected the phones of at least 51 people in the Catalonia region of Spain, according to Citizen Lab, a Canadian security organization at the University of Toronto. NSO Group Chief Executive Shalev Hulio told the New Yorker, which covered the hacks in depth, that Spain has legal procedures to ensure such use is legal, but Citizen Lab said Pegasus attacks targeted "members of the European Parliament, Catalan presidents, legislators, jurists," and some family members. Catalonia is seeking political independence from Spain, but Spanish police have cracked down on the independence movement.
The US government is one of the most powerful forces unleashed against Pegasus — even though the CIA and FBI were Pegasus customers, as reported by The New York Times in January. The US Justice Department has launched a criminal investigation, The Guardian said in February, after a whistleblower said NSO Group offered "bags of cash" for sensitive mobile phone data from a US tech firm, Mobileum. The spyware was found on the phones of at least nine State Department officials who were either based in Uganda or involved in matters associated with the African country, Reuters and The New York Times reported in December.
Pegasus is the latest example of how vulnerable we all are to digital prying. Our phones store our most personal information, including photos, text messages and emails. Spyware can reveal directly what's going on in our lives, bypassing the encryption that protects data sent over the internet.
Pegasus has been a politically explosive issue that's put Israel under pressure from activists and from governments worried about misuse of the software. In November, the US federal government took much stronger action, blocking sale of US technology to NSO by putting the company on the government's Entity List. NSO has suspended some countries' Pegasus privileges but has sought to defend its software and the controls it tries to place on its use. NSO Group didn't respond to a request for comment, and the Justice Department declined to comment.
Here's what you need to know about Pegasus.
What is NSO Group?
It's an Israel-based company that licenses surveillance software to government agencies. The company says its Pegasus software provides a valuable service because encryption technology has allowed criminals and terrorists to go "dark." The software runs secretly on smartphones, shedding light on what their owners are doing. Other companies provide similar software.
Hulio co-founded the company in 2010. NSO also offers other tools that locate where a phone is being used, defend against drones and mine law enforcement data to spot patterns.
NSO has been implicated by previous reports and lawsuits in other hacks, including a reported hack of Amazon founder Jeff Bezos in 2018. A Saudi dissident sued the company in 2018 for its alleged role in hacking a device belonging to journalist Jamal Khashoggi, who had been murdered inside the Saudi embassy in Turkey that year.
The New Yorker coverage details some of NSO Group's inner workings, including its argument that Pegasus is similar to military equipment that countries routinely sell to other countries, the company's tight ties to the Israeli government and its recent financial difficulties. It also revealed that NSO employees posted on the wall a detailed Google analysis of one Pegasus attack mechanism that concludes its NSO's abilities "rival those previously thought to be accessible to only a handful of nation states."
What is Pegasus?
Pegasus is NSO's best-known product. It can be installed remotely without a surveillance target ever having to open a document or website link, according to The Washington Post. Pegasus reveals all to the NSO customers who control it — text messages, photos, emails, videos, contact lists — and can record phone calls. It can also secretly turn on a phone's microphone and cameras to create new recordings, The Washington Post said.
General security practices like updating your software and using two-factor authentication can help keep mainstream hackers at bay, but protection is really hard when expert, well-funded attackers concentrate their resources on an individual. And Pegasus installations have employed "zero click" attacks that take advantage of vulnerabilities in software like Apple Messages or Meta's WhatsApp to silently install software.
Pegasus isn't supposed to be used to go after activists, journalists and politicians. "NSO Group licenses its products only to government intelligence and law enforcement agencies for the sole purpose of preventing and investigating terror and serious crime," the company says on its website. "Our vetting process goes beyond legal and regulatory requirements to ensure the lawful use of our technology as designed."
Human rights group Amnesty International, however, documents in detail how it traced compromised smartphones to NSO Group. Citizen Lab said it independently validated Amnesty International's conclusions after examining phone backup data and since 2021 has expanded its Pegasus investigations.
In September, though, Apple fixed a security hole that Pegasus exploited for installation on iPhones. Malware often uses collections of such vulnerabilities to gain a foothold on a device and then expand privileges to become more powerful. NSO Group's software also runs on Android phones.
Why is Pegasus in the news?
Forbidden Stories, a Paris journalism nonprofit, and Amnesty International, a human rights group, shared with 17 news organizations a list of more than 50,000 phone numbers for people believed to be of interest to NSO customers.
The news sites confirmed the identities of many of the individuals on the list and infections on their phones. Of data from 67 phones on the list, 37 exhibited signs of Pegasus installation or attempted installation, according to The Washington Post. Of those 37 phones, 34 were Apple iPhones.
The list of 50,000 phone numbers included 10 prime ministers, three presidents and a king, according to an international investigation released in mid-July by The Washington Post and other media outlets, though there's no proof that being on the list means an NSO attack was attempted or successful.
The episode hasn't helped Apple's reputation when it comes to device security. "We take any attack on our users very seriously," Federighi said. The company said it'll donate $10 million and any damages from the lawsuit to organizations that are advocating for privacy and are pursuing research on online surveillance. That's a drop in the bucket for Apple, which reported a profit of $20.5 billion for its most recent quarter, but it can be significant for much smaller organizations, like Citizen Lab.
Whose phones did Pegasus infect?
In the Catalonian situation, Pegasus found 63 phones were attacked and at least 51 were infected. That included the phone of Jordi Solé, a pro-independence member of the European Parliament, digital security researcher Elies Campo, and Campo's parents, according to the New Yorker.
In addition to Mangin, two journalists at Hungarian investigative outlet Direkt36 had infected phones, The Guardian reported.
A Pegasus attack was launched on the phone of Hanan Elatr, wife of murdered Saudi columnist Jamal Khashoggi, The Washington Post said, though it wasn't clear if the attack succeeded. But the spyware did make it onto the phone of Khashoggi's fiancee, Hatice Cengiz, shortly after his death.
Seven people in India were found with infected phones, including five journalists and one adviser to the opposition party critical of Prime Minister Narendra Modi, The Washington Post said.
And six people working for Palestinian human rights groups had Pegasus-infected phones, Citizen Lab reported in November.
What are the consequences of the Pegasus situation?
The US cut off NSO Group as a customer of US products, a serious move given that the company needs computer processors, phones and developer tools that often come from US companies. NSO "supplied spyware to foreign governments" that used it to maliciously target government officials, journalists, businesspeople, activists, academics and embassy workers. These tools have also enabled foreign governments to conduct transnational repression," the Commerce Department said.
Apple sued NSO Group in November, seeking to bar the company's software from being used on Apple devices, require NSO to locate and delete any private data its app collected, and disclose the profits from the operations. "Private companies developing state-sponsored spyware have become even more dangerous," said Apple software chief Craig Federighi. That suit came after Meta's WhatsApp sued NSO Group in 2019.
French President Emmanuel Macron changed one of his mobile phone numbers and requested new security checks after his number appeared on the list of 50,000 numbers, Politico reported. He convened a national security meeting to discuss the issue. Macron also raised Pegasus concerns with Israeli Prime Minister Naftali Bennett, calling for the country to investigate NSO and Pegasus, The Guardian reported. The Israeli government must approve export licenses for Pegasus.
Israel created a review commission to look into the Pegasus situation. And on July 28, Israeli defense authorities inspected NSO offices in person.
European Commission chief Ursula von der Leyen said if the allegations are verified, that Pegasus use is "completely unacceptable." She added, "Freedom of media, free press is one of the core values of the EU."
The Nationalist Congress Party in India demanded an investigation of Pegasus use.
Edward Snowden, who in 2013 leaked information about US National Security Agency surveillance practices, called for a ban on spyware sales in an interview with The Guardian. He argued that such tools otherwise will soon be used to spy on millions of people. "When we're talking about something like an iPhone, they're all running the same software around the world. So if they find a way to hack one iPhone, they've found a way to hack all of them," Snowden said.
What does NSO have to say about this?
NSO acknowledges its software can be misused. It cut off two customers in recent 12 months because of concerns about human rights abuses, according to The Washington Post. "To date, NSO has rejected over US $300 million in sales opportunities as a result of its human rights review processes," the company said in a June transparency report.
However, NSO strongly challenges any link to the list of phone numbers. "There is no link between the 50,000 numbers to NSO Group or Pegasus," the company said in a statement.
"Every allegation about misuse of the system is concerning me," Hulio told the Post. "It violates the trust that we give customers. We are investigating every allegation."
In a statement, NSO denied "false claims" about Pegasus that it said were "based on misleading interpretation of leaked data." Pegasus "cannot be used to conduct cybersurveillance within the United States," the company added.
Regarding the alleged infection of State Department phones, NSO Group didn't immediately respond to a request for comment. But it told Reuters it canceled relevant accounts, is investigating, and will take legal action if it finds misuse.
NSO will try to reverse the US government's sanction. "We look forward to presenting the full information regarding how we have the world's most rigorous compliance and human rights programs that are based the American values we deeply share, which already resulted in multiple terminations of contacts with government agencies that misused our products," an NSO spokesperson said.
In the past, NSO had also blocked Saudi Arabia, Dubai in the United Arab Emirates and some Mexican government agencies from using the software, The Washington Post reported.
How can I tell if my phone has been infected?
Amnesty International released an open-source utility called MVT (Mobile Verification Toolkit) that's designed to detect traces of Pegasus. The software runs on a personal computer and analyzes data including backup files exported from an iPhone or Android phone.
E.U. Officials Reportedly Targeted with
Israeli Pegasus Spyware
April 12, 2022

Senior officials in the European Union were allegedly targeted with NSO Group's infamous Pegasus surveillance tool, according to a new report from Reuters.
At least five individuals, including European Justice Commissioner Didier Reynders, are said to have been singled out in total, the news agency said, citing documents and two unnamed E.U. officials. However, it's not clear who used the commercial spyware against them or what information was obtained following the attacks.
NSO Group said in a statement shared with Reuters that it was not responsible for the hacking attempts, adding that the targeting "could not have happened with NSO's tools."
The intrusions are said to have come to light after Apple notified the victims of state-sponsored attacks last November as part of its efforts to stop the Israeli surveillance firm from targeting its customers.
That same month, the iPhone maker filed a lawsuit against NSO Group, seeking a court-issued injunction aimed at banning the company from using its products and services to develop and launch spyware attacks.
Apple called NSO Group as "notorious hackers — amoral 21st century mercenaries who have created highly sophisticated cyber-surveillance machinery that invites routine and flagrant abuse."
Pegasus, typically deployed through sophisticated "zero-click" exploits like FORCEDENTRY, grants its government and law enforcement customers complete access to a target's device, including their personal data, photos, messages, and precise location.
The widespread abuse of Pegasus to systematically spy on civil society in recent years has led the U.S. government to add NSO Group to its trade blocklist, in turn prompting Israel to restrict the number of countries to which local security firms can sell offensive hacking and surveillance tools.
In February 2022, the European Data Protection Supervisor called for a ban on the development and the use of Pegasus-like commercial spyware in the region, pointing out the technology's "unprecedented level of intrusiveness" that could endanger users' right to privacy.
But despite attempts to regulate the use of spyware, a forensic investigation released by Front Line Defenders last week found that the iPhone belonging to Suhair Jaradat, a Jordanian journalist and human rights defender, was hacked with Pegasus via a malicious WhatsApp message in December 2021, weeks after Apple initiated legal proceedings.
"The fact that the targeting we uncovered happened after the widespread publicity around Apple's lawsuit and notifications to victims is especially remarkable," the report said.
"A firm that truly respected such concerns would have at least paused operations for government clients, like Jordan, that have a widely publicized track record of human rights concerns and had enacted emergency powers giving authorities widespread latitude to infringe on civil liberties."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.

No comments:
Post a Comment